Cyber Security
 4 Slides
4 Slides
 File size: 16:9
File size: 16:9 
 Fonts: Lato Black, Calibri
Fonts: Lato Black, Calibri
 Supported version
PPT 2010, PPT 2013, PPT 2016
Supported version
PPT 2010, PPT 2013, PPT 2016
Product details
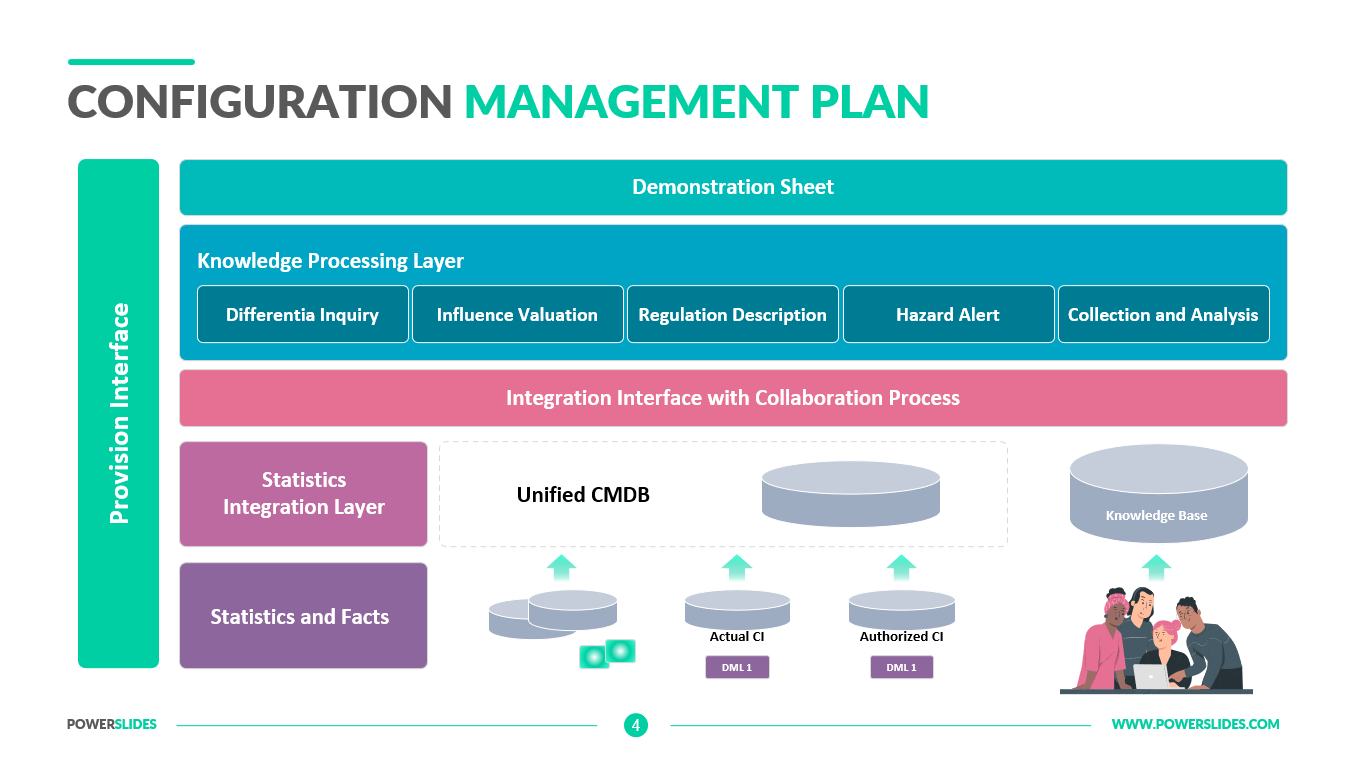
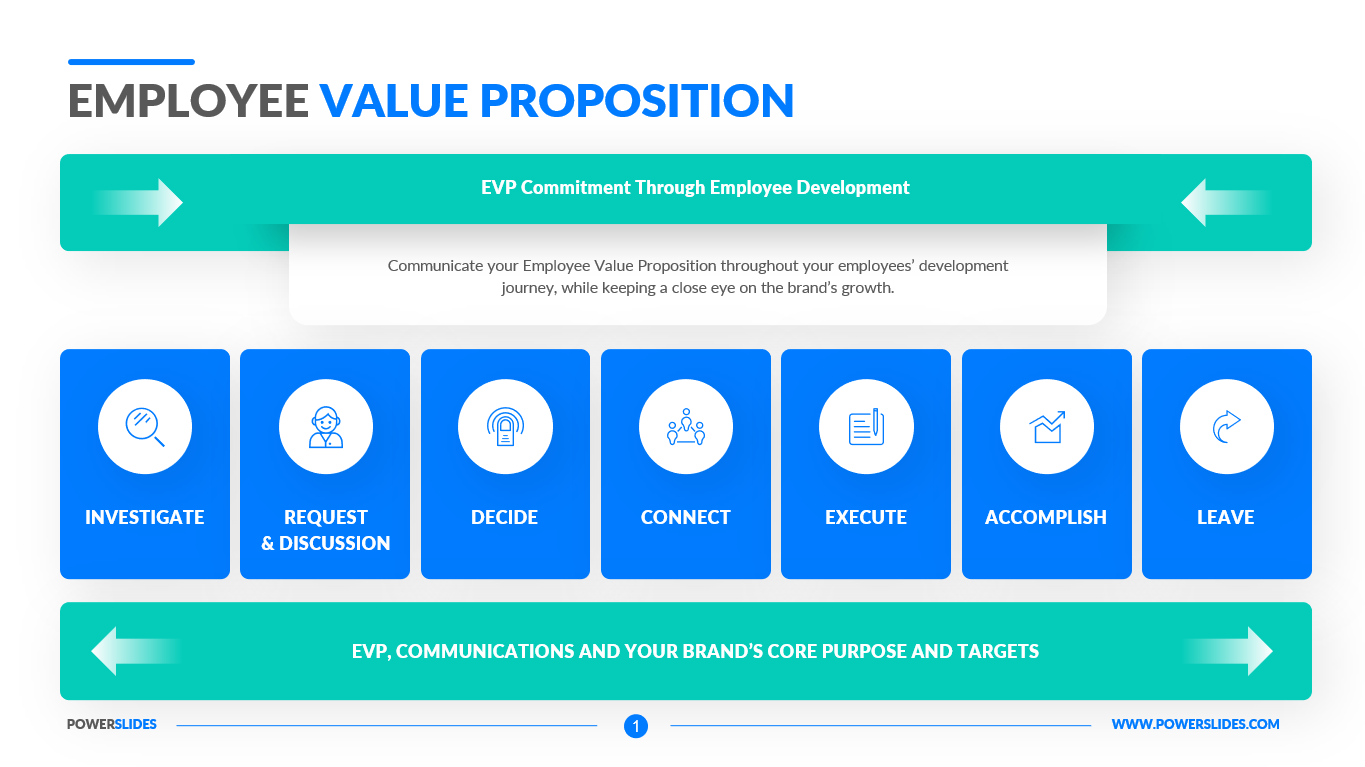
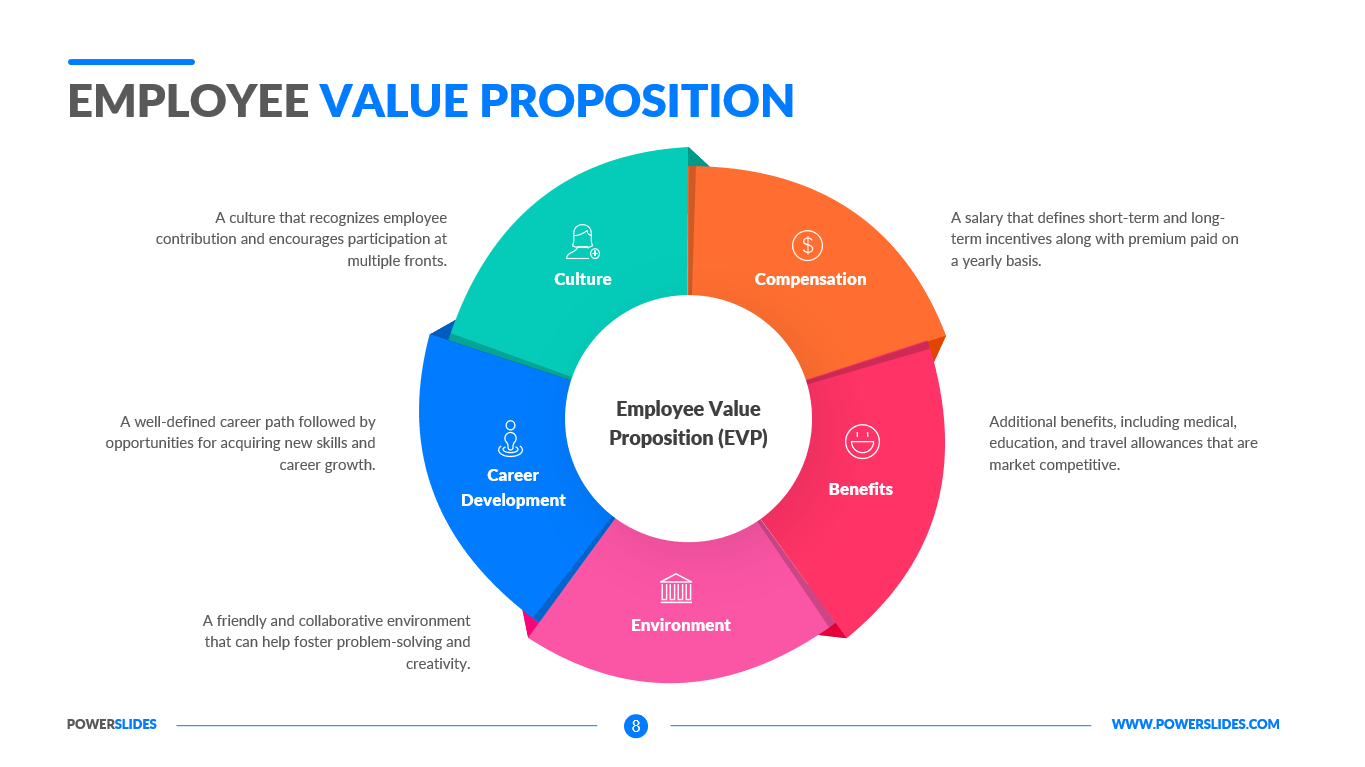
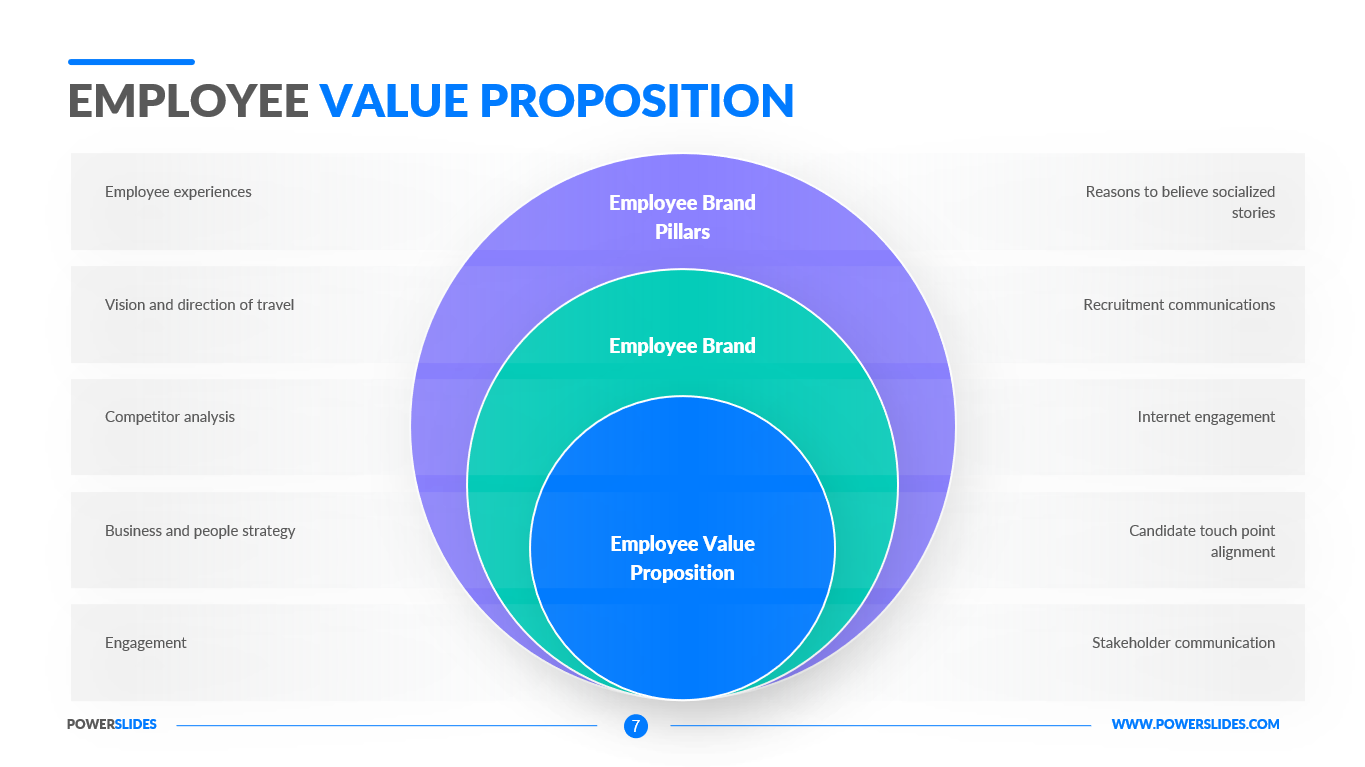
Cyber security refers to the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access. Cyber security may also be referred to as information technology security. Cyber security is important because government, military, corporate, financial, and medical organizations collect, process, and store unprecedented amounts of data on computers and other devices. A significant portion of that data can be sensitive information, whether that be intellectual property, financial data, personal information, or other types of data for which unauthorized access or exposure could have negative consequences. Organizations transmit sensitive data across networks and to other devices in the course of doing businesses, and cyber security describes the discipline dedicated to protecting that information and the systems used to process or store it. For an effective cyber security, an organization needs to coordinate its efforts throughout its entire information system. Elements of cyber encompass all of the following – network security, application security, endpoint security, data security, protecting company and customer information, identity management, database and infrastructure security, cloud security, mobile security. The most difficult challenge in cyber security is the ever-evolving nature of security risks themselves. Traditionally, organizations and the government have focused most of their cyber security resources on perimeter security to protect only their most crucial system components and defend against known treats. Today, this approach is insufficient, as the threats advance and change more quickly than organizations can keep up with. As a result, advisory organizations promote more proactive and adaptive approaches to cyber security. Following a cyber risk assessment, develop and implement a plan to mitigate cyber risk. This plan should encompass both the processes and technologies required to build a mature cyber security program. An ever-evolving field, cyber security best practices must evolve to accommodate the increasingly sophisticated attacks carried out by attackers. Combining sound cyber security measures with an educated and security-minded employee base provides the best defense against cyber criminals. While it may seem like a daunting task, start small and focus on your most sensitive data, scaling your efforts as your cyber program matures.
Cyber Security template is intended primarily for companies providing data protection services. You can use the slides from this template when preparing a presentation of your services for a client. For example, you can describe the main areas of data protection that your company provides. Also, the slides of this template will be useful for startups when preparing a description of the data protection process in a new software product. The slides from this template can be used by educators in their data protection courses. All slides in the template are made in a cool color scheme and have modern infographics. If necessary, you can change the slides to suit your corporate style. Cyber Security template will be a worthy addition to your collection of professional presentations.



 (4.50/ 5)
(4.50/ 5)