Security Risk Assessment
 4 Slides
4 Slides
 File size: 16:9
File size: 16:9 
 Fonts: Lato Black, Calibri
Fonts: Lato Black, Calibri
 Supported version
PPT 2010, PPT 2013, PPT 2016
Supported version
PPT 2010, PPT 2013, PPT 2016
Product details
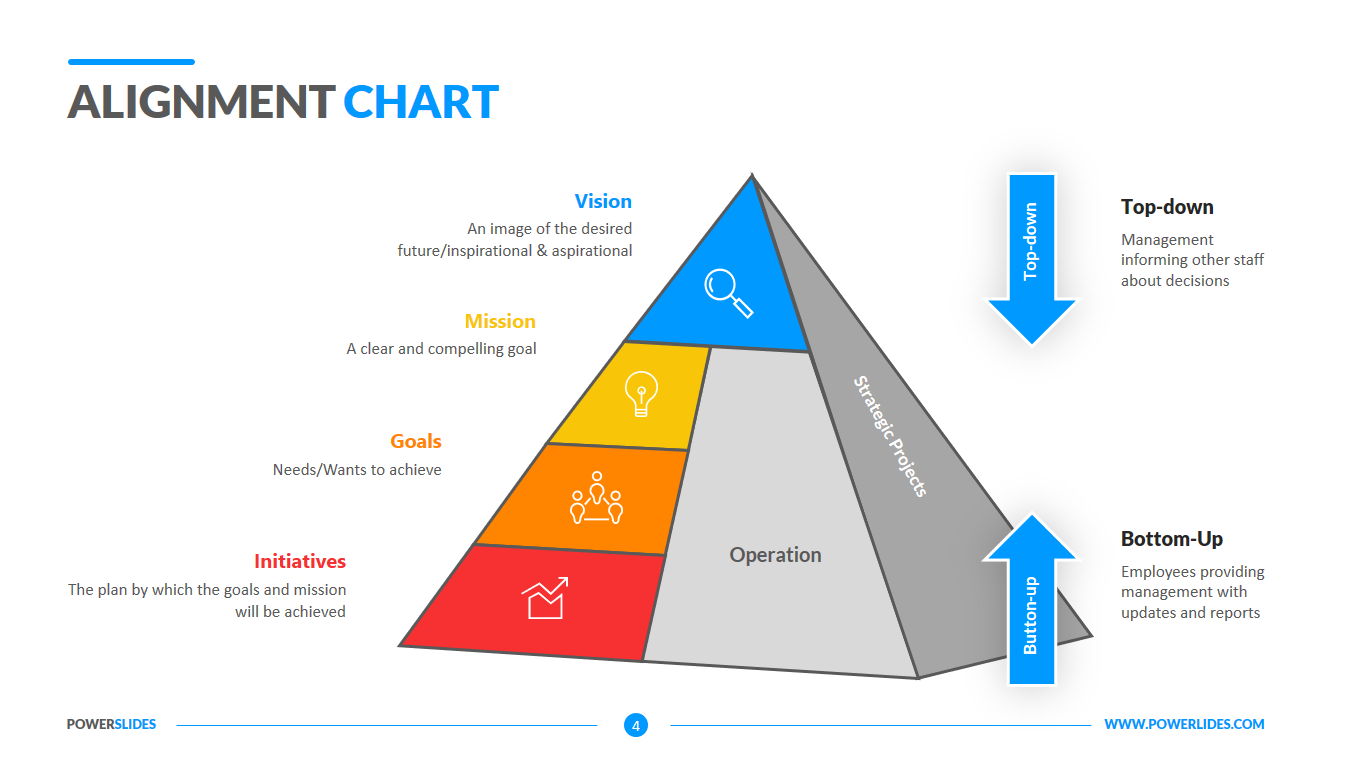
A Security Risk Assessment is an assessment that involves identifying the risks in your company, your technology and your processes to verify that controls are in place to safeguard against security threats. Security risk assessments are typically required by compliance standards, such as PCI-DSS standards for payment card security. Because of this, security risk assessments can go by many names, sometimes called a risk assessment, an IT infrastructure risk assessment, a security risk audit, or security audit.
Security Risk Assessments are performed by a security assessor who will evaluate all aspects of your companies systems to identify areas of risk. These may be as simple as a system that allows weak passwords, or could be more complex issues, such as insecure business processes. The assessor will typically review everything from HR policies to firewall configurations while working to identify potential risks.
For example, during the discovery process an assessor will identify all databases containing any sensitive information, an asset. That database is connected to the internet, a vulnerability. In order to protect that asset, you need to have a control in place, in this case it would be a firewall. You have now taken the first step in mitigating risk.
A Security Risk Assessment is vital in protecting your company from security risks. A security risk assessment provides you with the blueprint of risks that exist in your environment and gives you vital information about how critical each issue is. Knowing where to begin when improving your security allows you to maximize your IT resources and budget, saving you time and money.
Security Risk Assessments are deep dive evaluations of your company, or maybe even a specific IT project or even a company department. During the assessment, the goal is to find problems and security holes before the bad guys do. The assessment process should review and test systems and people, looking for weaknesses. As they are found, they are ranked based on how big of a risk they are to the company. The resulting report will identify systems that are working well and properly secured, and those that have issues. A Security Risk Assessment will typically have very specific technical results, such as network scanning results or firewall configuration results.
Crisis managers can use the slides of this template when preparing their strategy for getting the company out of losses. You can describe in detail what and what impact they have on each of the business processes in the company.
Analysts and stock traders can use the slides of this template to prepare analytical reports by categories of profitability and level of risk of investments in various stocks.
The Security Risk Assessment template will be useful for risk professionals, analysts and startup executives. All slides in this template have all the tools you need to build a professional presentation. You can customize colors, block sizes and infographics yourself. The Security Risk Assessment Template will be a worthy addition to your collection of professional presentations.